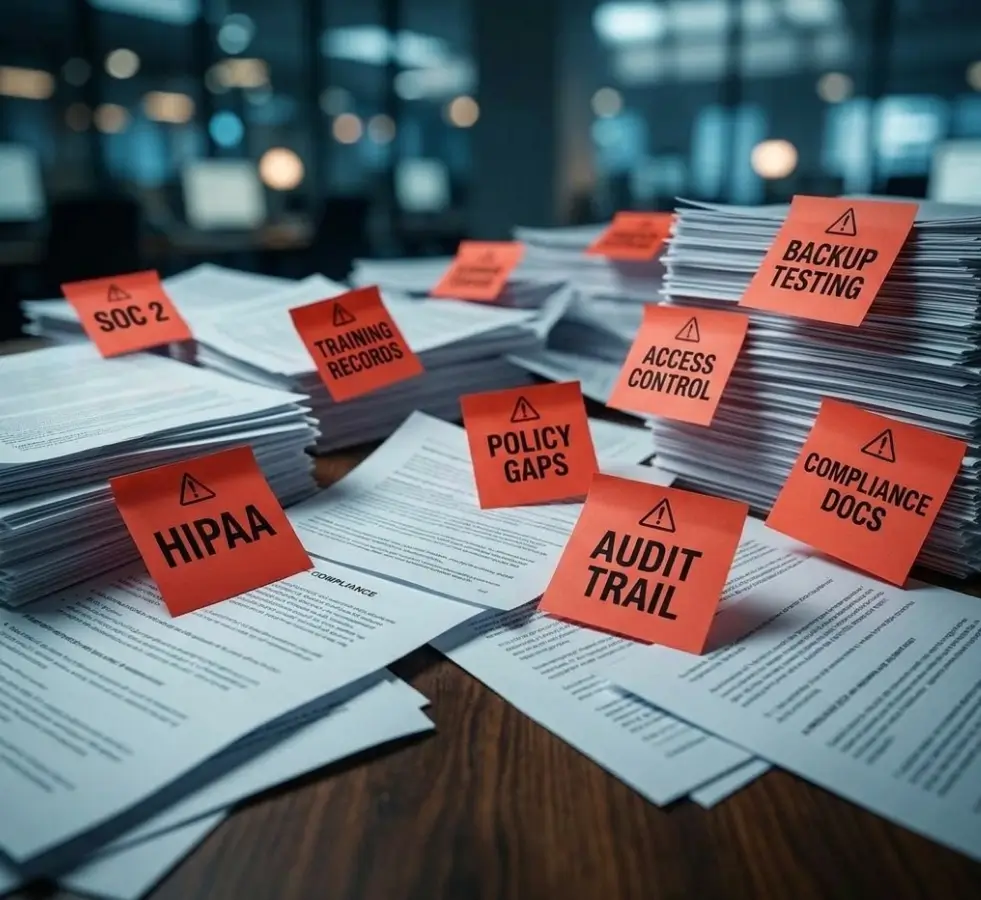
Regulations don’t wait, and auditors don’t accept “we’re working on it.” Whether you’re pursuing CMMC certification, preparing for a HIPAA audit, or building toward SOC readiness, the path forward starts with knowing exactly where you stand and having a structured plan to close the gaps before they cost you.
Your controls, access policies, encryption, and monitoring are evaluated against the framework that applies to you, whether CMMC, HIPAA, or SOC. You walk away knowing exactly where you stand.

Auditors want evidence, not just tools. Policies, procedures, and training records are reviewed against your framework requirements. Gaps in documentation carry the same weight as gaps in technology.

Each gap gets a specific, prioritized fix. The process is guided and hands on, not a checklist left for you to sort out alone. Your team knows what to address, in what order, and how each step maps to auditor expectations.

Once remediation is complete, your documentation is aligned and your controls are defensible. Regulated contracts, certification audits, and compliance reviews become manageable, not uncertain.



GiaSpace has been a constant partner of RVA. They have been instrumental in keeping us up to date and our IT systems compliant and operational. Thank you for always looking out for your customer and their needs.”


Rob helped me complete a Risk Assessment for my pharmacy for URAC Accreditation. He was extremely knowledgeable and helped me identify areas of weakness in the pharmacy as well as providing materials and vendors to strengthen it.”

Get the answers you need to move forward with clarity and stop second guessing your readiness.