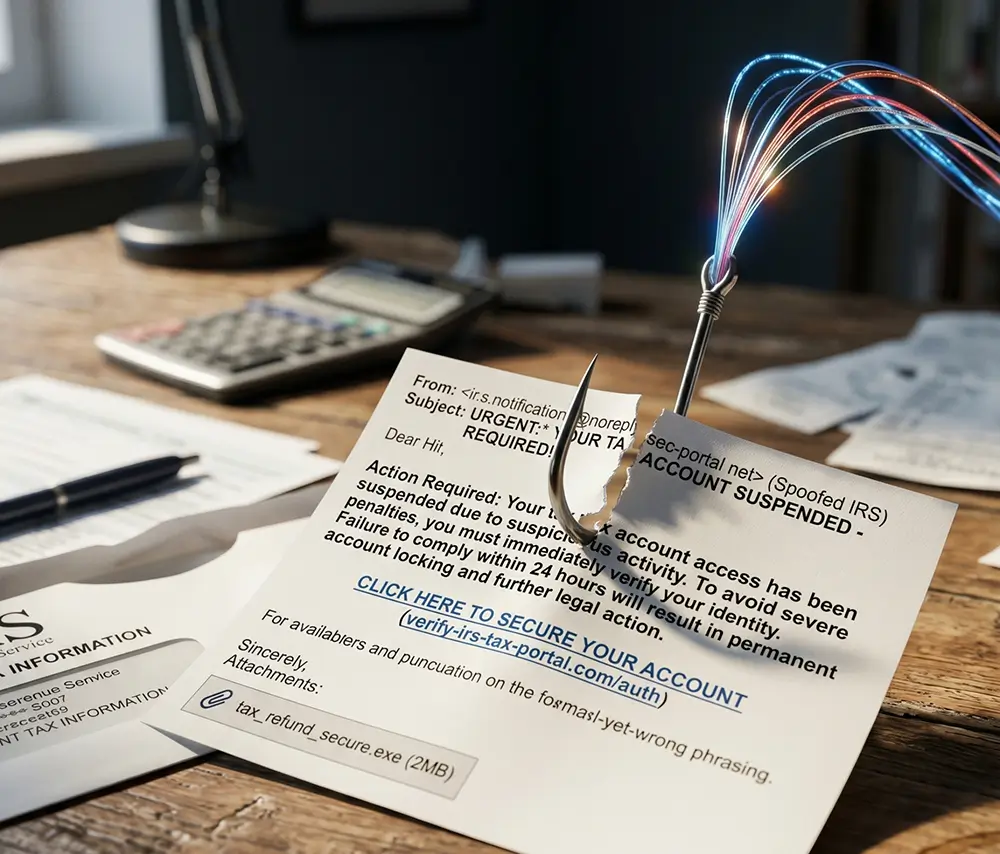
Email is still the fastest way into your systems, your data, and your people. The right email security solutions stop threats before they reach inboxes, protect sensitive information, and strengthen every layer of your cybersecurity strategy.



Thanks for your immediate response today! Two of our office emails were hacked and he jumped right in and changed our passwords. Thanks for all your assistance today!”

Get the answers you need to make informed and confident email security decisions.
The message is analysed by the help desk, not ignored or guessed at. If its malicious, action is taken immediately. If it’s safe, the employee gets a clear answer and can move on.